

The growing threat of cyber security in the renewable energy sector
The growing threat of cyber security in the renewable energy sector
Over the past decade, renewable energy has experienced unprecedented growth in Europe (International Energy Agency). But while standardisation and best practice proliferate as the industry is maturing, the area that has been consistently neglected is cyber security for renewable assets.
This article will identify why it is that cyber security for renewable assets has been somewhat neglected in the industry until only recently, the potential harm and threat this can cause your asset portfolio and solutions to mitigate such risks.
What is Cyber Security?
Cyber security refers to technologies, processes and controls that are designed to protect systems, networks, devices and data from attacks and unauthorised access.
With respect to renewable energy assets, each control with physical or on-line access presents a possible intrusion point. Access must be controlled, and data integrity must be maintained at each accessible point. Many renewable systems use advanced controls, digital sensors and network architectures near generation sources which should be adequately secured. Examples of components and systems that require consideration:
- Inverter control and monitoring
- CCTV
- Alarm systems (IDS and environmental)
- SCADA
- Communications
- Substation control system
- Field sensors
- Wind control stations
- Field weather and environmental data sensors
- Networking architecture and routers
Cyber Security in Renewable Energy Sector
Maturity across the renewable industry is low, leaving many asset owners vulnerable to attack.
- Cyber Security has not been a consideration during the design phase of most of the renewable assets operating today.
- Cheap, off the shelf SCADA and CCTV systems have been an industry norm.
- Key components were being selected without consideration for Cyber Security.
- There were no policies or regulations to follow.
- Buyers and their Technical Advisers were not scrutinising Cyber Security, neither during transactions, nor upon completion and acceptance.
As a result, there are a lot of renewable asset owners today in Europe who do not know where their data is stored, who has remote access to their systems, or how secure their connections are. This leaves renewable energy assets vulnerable and susceptible to cyber-attacks.
Cyberattack – A real threat
The threat of cyber-attacks is not hypothetical, with the first attack on renewable projects reported last year in the United States. sPower, a major solar and wind assets owner, experienced a series of lost connections between its main control centre and remote powergeneration sites. The brief, intermittent periods of downtime were determined to be the result of a Distributed Denial of Service (DDoS) attack. During cyber-attacks on the electricity grid in Ukraine in 2015/2016, hackers used remote control of SCADA and substation infrastructure. Although this time the attack was not on renewable energy infrastructure, it exploited the vulnerabilities in the system that we are also exposed.
Cyberattacks – Potential Consequences
The consequences of a cyber-attack on renewable assets will vary and will depend heavily on the type of attack. Some of the consequences may be:
- Loss of visibility and data
- Financial loss (e.g. if cyberattack leads to loss of generation, or damages any part of the system)
- Reputational damage (e.g. if cyberattack becomes public, revealing company’s low security measures)
- Loss of opportunities (e.g., virtual power plants require high cyber security standards, potential buyers may require high level of cyber security)
- Increase of insurance premium (cyber security as a condition to offer cover)
Are you confident that your Cyber Security measures will protect you against these consequences?
Solutions
When deciding on your Cyber Security strategy as an operator, you should weigh the cost of recovery from a cyber-attack against the cost of implementing additional security measures. Some measures are relatively inexpensive and easy to implement, such as putting in place policies and assuring that the software you are using has been updated. Regulating remote access to systems is another step that can be taken. However, due to a complex and highly specialised nature of Cyber Security, ad hoc solutions may not always be sufficient.
Setting your Cyber Security strategy should start with a comprehensive assessment of the current state of Cyber Security across your portfolio. Such audits should assess the current policies, processes, practices, systems, infrastructure, suppliers along with providing recommendations for further actions.
A well planned and managed Cyber Security strategy can decrease your vulnerabilities and the risk of a cyber-attack.
Minimum Requirements:
The world of Cyber Security is vast, so here are our recommended minimum requirements to get you started:
- Implement a Secure Password policy: all factory settings should be changed, each plant should have a unique password, passwords should be shared with a limited number of staff, changed frequently, and shared only based of need; staff should be trained to ensure they understand both IT and the policy.
- Loggers should be protected by a firewall and shouldn’t be accessible directly via internet
- Use of Virtual Private Networks is necessary
This list, although not exhaustive, is a good representation of high impact actions which asset owners should implement.
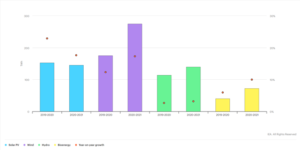
Demystifying the Cybersecurity Cost
Range of Cost that someone should expect for:
- Policy creation
- Site and equipment inspections
- Risk mitigation strategy
- Annual reviews and inspections
What Greensolver can do for you
Cyber security for renewable assets is a highly specialised area needing expert advice. In recognition of this need, Greensolver has partnered with Cyber Security professionals to provide the best advice to wind and solar project owners.
Whether you need advice on password policy, a VPN set up, or a comprehensive assessment on your existing Cyber Security, we can offer advice that is based not only on expert IT knowledge but also on a deep understanding of the lifecycle of renewable energy plants, and the market and stakeholders involved in it. And despite the highly sophisticated nature of the topic, the cost of audits and remedial works are not prohibitive.
Contact us if you would like assistance securing your assets from potential cyber attacks.
 https://www.iea.org/data-and-statistics/charts/renewable-electricity-generation-increase-by-technology-2019-2020-and-2020-2021
https://www.iea.org/data-and-statistics/charts/renewable-electricity-generation-increase-by-technology-2019-2020-and-2020-2021